Static IP Address: How It Works, When to Use It, and What It Offers
A static IP address is a fixed, unchanging numerical label assigned to a device or server on a network. Unlike dynamic addresses, a static IP remains the same each time the device connects to the internet or a local network. This type ...

NIS2 Directive Explained: What’s New in Cybersecurity Regulations and Audits
As cybersecurity threats grow more frequent and sophisticated, the European Union is responding with stricter, more expansive regulations. The latest evolution is the NIS2 Directive—a significant update to its original Network and Information Security Directive (NIS1). For organizations operating in ...

What Residential Proxies Providers Deliver Today
What Top Residential Proxy Providers Offer Today
Residential proxies providers offer access to proxy IPs from residential internet connections. These IPs, from real devices, enable anonymous, geo-targeted, and undetectable online activity. Their core function is to route user requests through multiple legitimate, ...

Building a Unified Data Management Strategy with Lineage Integration
In today's data-driven world, databases play a crucial role in storing, managing, and retrieving vast amounts of information. As organizations continue to generate and rely on data for decision-making, the need for a robust data management strategy becomes increasingly important. ...

Why is a German VPS the best choice for traders and gamers?
Virtual Private Servers (VPS) have become an indispensable tool for many users, especially traders and gamers. However, among the various options, the German VPS stands out as one of the best choices for numerous reasons. In this article, we will ...

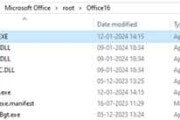
Best Cyber Forensics Software in 2026: Top Tools for Windows Forensics and Beyond
In the ever-evolving world of cybersecurity, cyber forensics software has become indispensable for investigating digital crimes, recovering lost data, and analyzing cyber threats. As we step into 2026, the demand for advanced forensic tools has skyrocketed. Windows forensics is no ...

Data Security Challenges in Embedded Systems for Big Data Applications
In today's interconnected world, embedded systems play a pivotal role in managing and processing vast amounts of data across various applications. As these systems become increasingly integral to big data environments, ensuring their security has become a paramount concern. Ecrin ...

Top 7 Challenges in AI and Intelligent Operations
Artificial Intelligence (AI) has emerged as a key element of Intelligent Operations of an organization. The reason is because it allows them to fully promote automation of processes, the optimization of resources and workflows, as well as the application of ...
How to Fix the .pst File Problem: Empty PST File with Large Size
Microsoft Outlook is undeniably the most popular email client for work communication. Its pillars of strength are its file formats—OST and PST. Both these files store mailbox content like email messages, attachment, messages, etc. The PST (Personal Storage Table) files ...

How Passkeys Support Zero Trust in Big Data Environments
In an age of massive data flows and constantly evolving cyber threats, keeping security protocols robust is no longer an option; it's a must. By their very nature, big data environments have to process and store unimaginable volumes of sensitive ...
























